1. Black hat
A person who hacks for illegal purposes, usually for economic gain. They enter the secure network to destroy, redeem, modify or steal data, or make the network unavailable to authorized users. The name comes from the fact that villains in old-fashioned black-and-white western films are easy to be recognized by film viewers because they wear black styson and "good people" wear white hats.

2. Back door
The "pipes" hidden in the computer system bypass the orthodox protection of login and password, so that they are basically ineffective in protecting data.
3. Brute force attack
Hackers conduct highly intensive automatic search for every possible password in the system, so as to destroy security and obtain access to the computer.
4,Doxing
Discover and publish the identity of Internet users by viewing their details online. Complete glossary of hacker terms
5. A gray hat
A person who performs hacker attacks, but not for personal or economic interests. One example is hacking, which is carried out as part of a broader political protest. Activists make an organization's policies or official views embarrassing or humiliating as a curse.
6,IP
Internet protocol address - the identifier or fingerprint of the computer. This is used to identify people using the device, track their activities, or display their location.
7. Key record
Track which keys computer users press so that hackers can record login codes and passwords into the system.
8. Malware
A program designed to control or steal computer data.
① More than 200 e-books of network security series
② Network security standard question bank data
③ Project source code
④ Introduction to network security basics, Linux, web security, attack and defense videos
⑤ Network Security Learning Route
⑥ Poke this Free access
9. Phishing
By sending them an email that appears to be from a real person or organization, repeat someone to provide you with their personal information, such as passwords, bank account details (such as PIN numbers), and credit card details.
10. Cheat
Change the real email so that it now appears to come from other places, such as your bank, and provide false instructions. If you follow these instructions, it will endanger the security of your data.
11. Spyware
This is a kind of "malware", which is programmed to be unnoticed on the computer and quietly send data to hackers.
12. Whaling
Phishing is aimed at the senior management of the organization. Hackers pursue economic interests or participate more in political undertakings. Whaling can be used to collect sensitive or extremely embarrassing information about individuals, such as wages, bonuses, private addresses, e-mail and telephone numbers.
13. White hat
Hackers use their skills for social welfare or help organizations by exposing vulnerabilities in their IT systems. This is the reverse side of a black hat.
14. Loopholes
Vulnerability refers to the defect or improper configuration in the software, hardware or communication protocol in the information system,
Thus, the attacker can access or destroy the system without authorization, resulting in the security risk of the information system.
Common vulnerabilities include SQL injection vulnerability, weak password vulnerability, remote command execution vulnerability, permission bypass vulnerability, etc.
15. Malicious program
Malicious programs are installed and executed in the information system without authorization to achieve improper purposes
Procedures for.
1.Trojan horse Trojan horse (Trojan horse for short) is a malicious program whose main purpose is to steal user's personal information and remotely control user's computer. It is usually composed of control end and controlled end. Because it sneaks into the user's computer like a spy, it is very similar to the "Trojan horse" tactics in the war, so it is named Trojan horse. According to their functions, Trojan horse programs can be further divided into 7 categories: number stealing Trojan horse, online banking Trojan horse, secret stealing Trojan horse, remote control Trojan horse, traffic hijacking Trojan horse, downloader Trojan horse and other Trojan horses. Number stealing Trojan horse is a Trojan horse used to steal users' e-mail, online games and other accounts. Online banking Trojan horse is a Trojan horse used to steal users' online banking, securities and other accounts. Secret stealing Trojan horse is a Trojan horse used to steal sensitive files or data from the user's host. Remote control Trojan horse is a Trojan horse that obtains the permission of host administrator by improper means and can manipulate the user's host through the network. Traffic hijacking Trojan horse is a Trojan horse used to hijack the traffic of users' network browsing to the site designated by the attacker. Downloader Trojan horse is a Trojan horse used to download more malicious code to the user's host and run it to further manipulate the user's host. two.Zombie program zombie program is a malicious program used to build a large-scale attack platform. According to the communication protocol used, zombie programs can be further divided into IRC Zombie programs HTTP Zombie programs P2P Zombie programs and other zombie programs fall into four categories. three.Worms are malicious programs that can replicate and spread widely and occupy system and network resources. Worms can be further divided into mail worms, instant messaging worms U Disk worms, exploit worms and other worms. four.Virus is a malicious program that spreads by infecting computer files to destroy or tamper with user data and affect the normal operation of information system. five.Blackmail software blackmail software is a kind of malicious software used by hackers to hijack users' assets or resources and extort money from users on this condition. Blackmail software usually encrypts user data or user equipment or changes the configuration to make it unavailable, and then sends blackmail notice to the user, asking the user to pay for decryption password or get the method to restore the normal operation of the system. six.Mobile Internet malicious programs mobile Internet malicious programs refer to executable files, program modules or program fragments that are installed and run in the mobile terminal system without the user's knowledge or authorization to achieve improper purposes, or that violate relevant national laws and regulations. According to the classification of behavior attributes, mobile Internet malicious programs include 8 types: malicious fee deduction, information theft, remote control, malicious communication, tariff consumption, system damage, deception and fraud and rogue behavior. seven.Other malicious programs not included in the above categories.
Classification by main purpose of malware
With the development of hacker underground industry chain, some malicious programs on the Internet also have the above classification
It has multiple functional attributes and technical characteristics, and continues to develop. In this regard, we will follow the main purpose of malicious programs
Refer to the above definition for classification.
1.Botnet botnet is a computer group centrally controlled by hackers. Its core feature is that hackers can manipulate the host infected with Trojan horse or zombie program to perform the same malicious behavior through one to many commands and control channel, such as distributed denial of service attack on a target website at the same time, or send a large number of spam, etc. two.Denial of service attack denial of service attack is to send dense attack packets to a target information system or perform specific attack operations in order to cause the target system to stop providing services. three.Web page tampering web page tampering is the malicious destruction or change of web page content, which makes the website unable to work normally or abnormal web page content inserted by hackers. four.Web page counterfeiting web page counterfeiting is an attack way to deceive users by constructing pages highly similar to a target website. Phishing website is a common form of web page counterfeiting, which is often spread by means of spam, instant chat, mobile phone short message or web page false advertisement. Users may disclose their account, password and other personal privacy after visiting phishing website. five.Website backdoor website backdoor incident refers to the attack form that hackers upload a remote control page in a specific directory of the website, so that they can secretly and remotely control the website server through the page. six.Spam refers to e-mail that is forcibly sent to the user's mailbox without the user's permission (irrelevant to the user). seven.Domain name hijacking domain name hijacking is to intercept domain name resolution requests or tamper with the data on the domain name server, so that users return false information when accessing relevant domain names IP Address or user request failed. eight.Route hijacking route hijacking is to change the route information by deception, so that the user cannot access the correct target, or cause the user's access traffic to bypass the path set by the hacker to achieve an improper purpose.
16. The difference between viruses and Trojans
Viruses: The virus we usually say refers to an infectious virus, which is a set of computer instructions or program code inserted by the programmer into the computer program that destroys the computer function or data, can affect the use of the computer and can replicate itself. It has transmissibility, concealment, infectivity, latency, excitability, expressiveness or destructiveness. Life cycle of general virus: development period→Infectious period→incubation period→Paroxysmal period→Discovery period→Digestive period→Extinction period. It has many similarities with biological viruses, such as biological virus characteristics such as self reproduction, mutual infection and activation and regeneration. Trojan horse: Trojan horse virus is named after the famous "Trojan horse scheme" in the Trojan War in ancient Greece. Here you can baidu by yourself. It's a very interesting story. Trojan viruses are generally sent out through e-mail attachments, bundled in other programs, and control another computer through a specific program (Trojan horse program). There are usually two executable programs: one is the control end, and the other is the controlled end. "Trojan horse" program is different from ordinary viruses. It will not reproduce itself, nor "deliberately" infect other files. It will modify the registry, reside in memory, install backdoor programs in the system, and boot and load the attached Trojan horse. The attack of Trojan virus needs to run the client program in the user's machine. Once it occurs, a back door can be set to regularly send the user's privacy to the address specified by the Trojan program. Generally, a port that can enter the user's computer is built at the same time, and the computer can be controlled arbitrarily for illegal operations such as file deletion, copy and password change. Draw a key point and tell the difference between the two: 1, Viruses can infect, but Trojans can't; 2, After the virus invades the computer, it will feel, but the Trojan horse will not. The main reason is to carry out the follow-up "work"; 3, Viruses are mainly known for "destruction", while Trojans are mainly used to steal user information. At this point, I would like to add some knowledge about worms. The essential difference from trojan virus is that worm virus is a malicious program that can use system vulnerabilities to spread itself through the network. It does not need to be attached to other programs, but exists independently. When the scale is formed and the propagation speed is too fast, it will greatly consume network resources, resulting in large-area network congestion and even paralysis, which is much more terrible than trojan virus.
17. Honeypot
(1) Honeypot technology is essentially a technology to cheat the attacker. By arranging some hosts, network services or information as bait, the attacker can be induced to attack them, so that the attack behavior can be captured and analyzed, the tools and methods used by the attacker can be understood, and the attack intention and motivation can be inferred, It enables the defender to clearly understand the security threats they are facing, and make money through technical and management means
(2) Honeypot is like an intelligence collection system. Honeypot seems to be a deliberate target for people to attack and lure hackers to attack. Therefore, the attacker can know how the attacker succeeds, keep abreast of the latest attacks and vulnerabilities launched against the server, eavesdrop on the connections between hackers, various tools used by mobile phone hackers, and master their social networks
18. Dark net
The Internet consists of three layers of networks Presentation layer network Deep net Dark net
How to access the dark net
LAN -- > (surface network) indicates layer network -- > deep network -- > dark network
Surface web is a common website that can be accessed, such as:Baidu,Tencent video... It's still difficult to access the dark network!
Dark net is a subset of deep net
(1) Dark net and deep net cannot be mixed together,90% of the Internet comes from Shenwang(2)Deep net:Cannot be searched by search engine,It can only be accessed through special software!for example:qq/Wechat and other chat tools can be called Shenwang,Can't be found by search engines(3) Dark net is a subset of deep net(branch),Not directly accessible,A specific browser is required,Its domain names are in the form of.onion As a suffix
-Difference between deep net and dark net
(1) The role of the dark network invented by the United States is to exchange information between spies in the dark network in an anonymous way
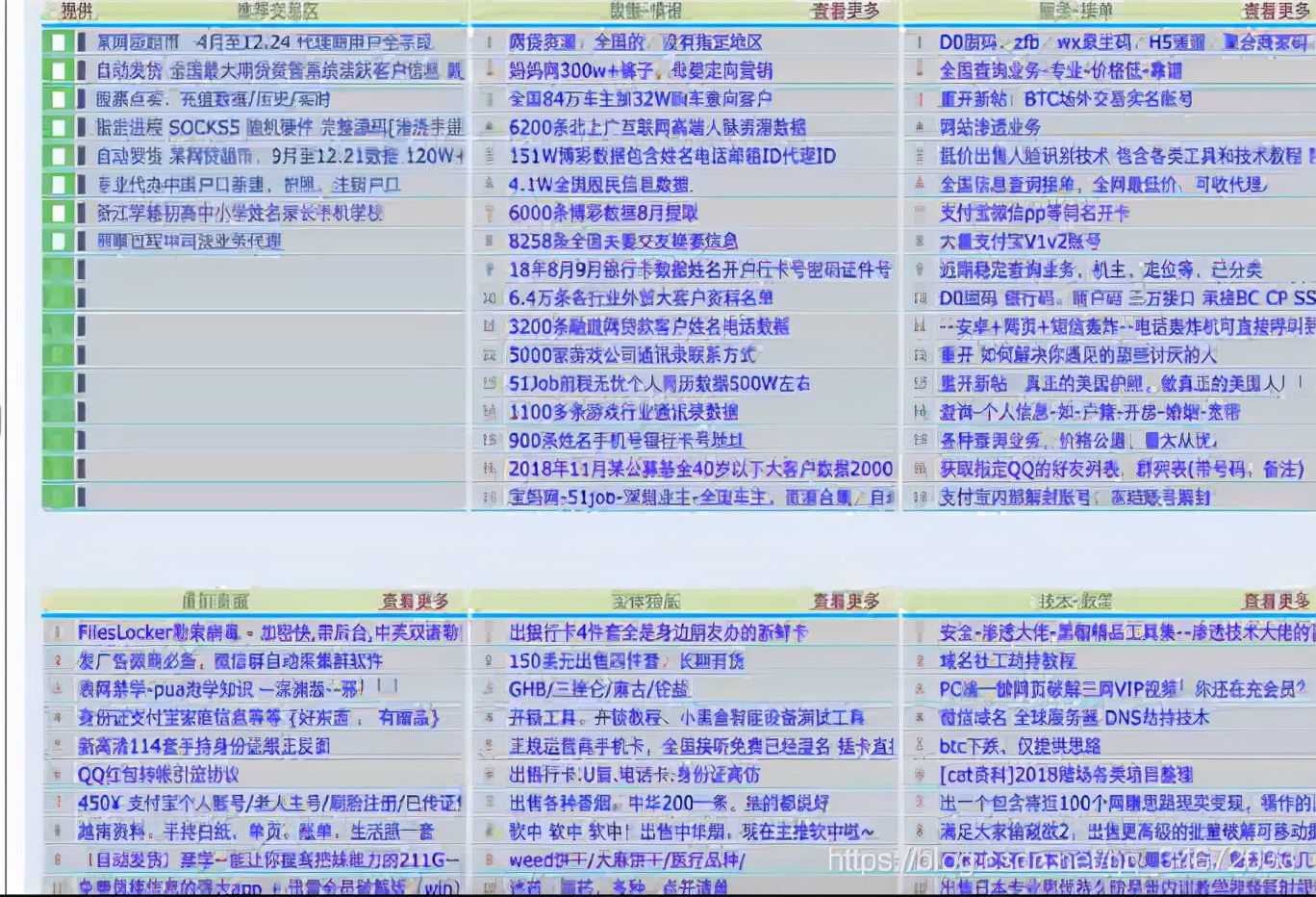
(2) There are a lot of data information stolen from trading and various public opinion information in the dark network
19. Avoid killing
Killing free is to avoid the scanning and killing of anti-virus software and make anti-virus software a decoration. In addition, killing free technology will bring us more, which will be a leap in thought and the growth of technology
20. APT attack
APT(advanced Persistent Threat) refers to the supply form of advanced persistent threat, which uses advanced attack means to carry out long-term persistent network attacks on specific targets
(1)China is APT The main victim of the attack (2)APT The attack is usually a country/A group to support the team to attack and steal scientific research achievements and data (3)Once APT It will be difficult to escape after the attack is targeted.
21,Exploit/POC
Exploit (exploiter)
Exploit/Exp English means to use,It is vulnerability exploitation in the eyes of hackers.There are loopholes, not necessarily Exploit(utilize),have Exploit There must be a loophole
POC (proof of vulnerability)
Proof of concept(English:proof of concept:abbreviation POC)It is a short and incomplete implementation of some ideas,To prove its feasibility,The principle of picking up rice,Its purpose is to verify some concepts or theories,Proof of concept is usually considered as a milestone implementation prototype.sketch:There is a loophole in the certification program,But we can't take advantage of this loophole
22. Intranet penetration
What is intranet penetration? Why intranet penetration? Intranet penetration is to change an environment for penetration Some important data/data/The code will be put into the intranet server or the company's internal developer computer,Therefore, intranet scanning is required/infiltration, Intranet penetration requires more randomness and breakthrough, and the situation is more complex. It involves a wide range of knowledge,There are also many attack techniques 0
23. Social psychology
In computer science, social engineering refers to the way of legally communicating with others to affect their psychology, make some actions or disclose some confidential information. It is usually considered as an act of cheating others to collect information / cheat and invade computer systems. In the common law system, this act is generally considered to infringe the right of privacy!
Social work Library
Social work Library (1)A tool in social engineering,Integrate the leaked or infiltrated data into the social work database,Search query usage, (2)The complex social work database can be integrated by using the infiltrated or leaked data,To find out someone's mobile phone number/Room opening record/Various passwords, etc
24. Google hacker
Google hacking uses search engines such as Google to locate security risks and vulnerable points on the Internet
There are generally two types of attacks that are easy to find on the Web:
(1) Software vulnerabilities
(2) Wrong configuration
Although some experienced intruders aim at some special systems and try to find vulnerabilities that will allow them to enter, most intruders start from specific software vulnerabilities or from the wrong configurations of ordinary users. In these configurations, they already know how to invade and preliminarily try to find or scan the systems with such vulnerabilities, Google is of little use to the first attacker, but it plays an important role to the second attacker!
Google hackers learn links and play a role in information collection in terms of penetration!
25. Take off your pants
Homophonic correspondence of pants off
De library means to obtain the database of the website, member information or information they need through illegal means
A simple understanding is to download the information of the other party's database!
26. Right raising
After getting the webshell, upgrade from an ordinary user to an administrator!
27. 0 (zero) day attack
0day attack, an attack on computer software
(1) In the computer field, zero day exploit / zero day / 0-day vulnerabilities usually refer to security vulnerabilities that have not been patched,
A vulnerability discovered by itself and not published is called 0 day
(2) Zero Day attack or zero day attack refers to an attack using this vulnerability. The person who provides the details of the vulnerability or exploits the program is usually the discoverer of the vulnerability,
Zero Day vulnerabilities are a great threat to network security. Therefore, zero day vulnerabilities are not only the favorite of hackers, but also an important parameter to evaluate the technical level of hackers!
28. Side station / section C
Side station
Other sites on the server where the target site is located,Then find a way to cross into the directory of the real target site