explain
This blog is updated every Friday.
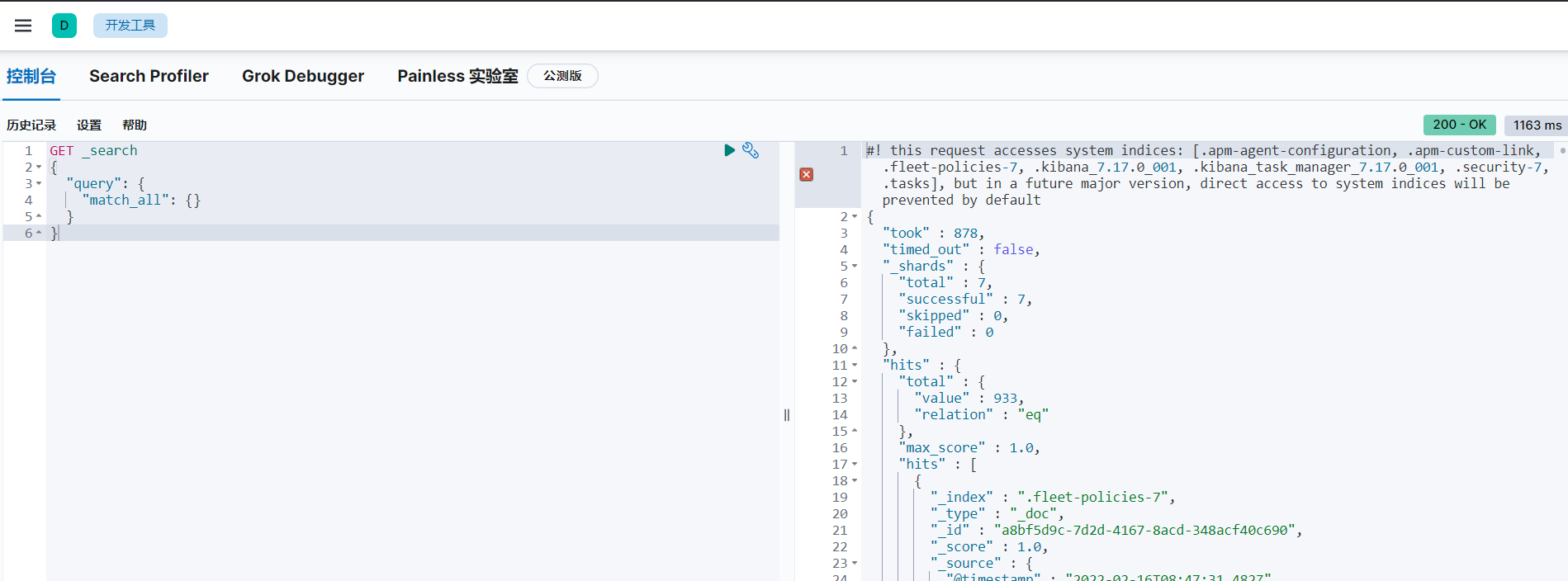
Based on the original Elasticsearch installation, this paper adds plug-in x-pack user authority authentication and Kibana page management to enrich the use scenarios of Elasticsearch.
The installation is divided into three levels
- Normal installation, only Kibana is enabled, and x-pack is not enabled
- User authentication, start x-pack, Kibana automatically starts user management.
- https encryption increases data security for Elasticsearch and Kibana.
share
data
- Elasticsearch Official website offer , demo version 7.17.0
- Software download Various versions are officially available, including ordinary version, Elastic Version (ecctl), No Jdk version, OSS version and OSS No Jdk version
- Security configuration file
- Charge for each version information
- elastic CSDN official blog website
Home page service
- kibana homepage address: http://localhost:5601/app/home#/
- Elasticsearch interface address: http://localhost:9200/
install
Normal installation
system configuration
- Modify the maximum file description size of the system. The default is 4096 and the minimum is 65535. Modify the file: / etc / security / limits The default additions to conf are as follows:
* soft nofile 65535 * hard nofile 65535 * soft nproc 65535 * hard nproc 65535
- Modify the maximum virtual memory of the system. The default is 65535 and the minimum is 262144. Modify the file: / etc / sysctl Conf, add content at the end: VM max_ map_ Count = 262144, immediate command: / sbin/sysctl -p
Install software
From the official website download Version 7.17, unzip it to the installation directory.
- The installation startup user must be a non root user.
# Create installation directory mkdir /usr/local/elasticsearch # Unzip the installation package cd /usr/local/elasticsearch tar -zxvf elasticsearch-7.17.0-linux-x86_64.tar.gz tar -zxvf kibana-7.17.0-linux-x86_64.tar.gz #Create user useradd user # to grant authorization chown -R user: /usr/local/elasticsearch/ ####### Switch to the new user, and subsequent operations will be completed with this user#### su user
software configuration
elasticsearch.yml
- Edit file: config / elasticsearch YML, set as follows
# ---------------------------------- Cluster ----------------------------------- # Cluster name cluster.name: my-application # The collection of primary nodes in the cluster cluster.initial_master_nodes: ["node-1"] # # ------------------------------------ Node ------------------------------------ # # Use a descriptive name for the node: # Node name node.name: node-1 # ----------------------------------- Paths ------------------------------------ # Set data storage directory path.data: /usr/local/elasticsearch/elasticsearch-7.17.0/data # Set the directory of logs path.logs: /usr/local/elasticsearch/elasticsearch-7.17.0/logs # ---------------------------------- Network ----------------------------------- # # Only localhost is accessed by default. Configure the current server ip to allow ip access network.host: 192.168.10.200 # Service port, default to 9200 http.port: 9200
jvm.options
Edit file: config / JVM Options fill in the following
-Xms1g -Xmx1g
Start and verify
- Start: software root directory execute command: bin/elasticsearch
- Verification: browser open web address: http: / / server ip:9200
Install kibana
Unzip the installation package and modify the configuration file: VI config / kibana YML, specify Elasticsearch address:
# kibana service address, accessible only by localhost by default server.host: "192.168.10.200" # Elastic search service address elasticsearch.hosts: ["http://192.168.10.200:9200"] # The system language defaults to English and changes to Chinese i18n.locale: "zh-CN"
Just run the startup software. Command: bin/kibana, login address: http://ip:5601
User authentication
Turn on x-pack verification
Edit file: config / elasticsearch YML, set the following:
# Enable xpack xpack.security.enabled: true # Ensure that nodes do not inadvertently connect to other clusters that may be running on the network discovery.type: single-node # Turn on transport layer ssl encryption. The service cannot be started without turning on xpack.security.transport.ssl.enabled: true
be careful:
- Once x-pack is enabled, TLS/SSL encrypted transmission must be enabled, otherwise there will be log errors as follows:
Transport SSL must be enabled if security is enabled on a [basic] license. Please set [xpack.security.transport.ssl.enabled] to [true] or disable security by setting [xpack.security.enabled] to [false]
Create content user
- Start Elasticsearch: bin/elasticsearch
- Create a new terminal window and create a built-in user.
# Custom password bin/elasticsearch-setup-passwords interactive # Randomly generated password bin/elasticsearch-setup-passwords auto # The random generation results are as follows Changed password for user apm_system PASSWORD apm_system = h1d0q4mfPvbgxqQeLERj Changed password for user kibana_system PASSWORD kibana_system = OzKzbRb84YtgyvoXkvXO # Log in to Kibana account Changed password for user kibana PASSWORD kibana = OzKzbRb84YtgyvoXkvXO Changed password for user logstash_system PASSWORD logstash_system = kLFsukpLcsyGsqNFGMuW Changed password for user beats_system PASSWORD beats_system = ESvQWN3jbM4s7f78CU72 Changed password for user remote_monitoring_user PASSWORD remote_monitoring_user = KvLoRUhEKutOXrL23ZWL Changed password for user elastic PASSWORD elastic = Hm3pZkPVsEpwPC7Kj9QA
be careful:
- After setting the password for the user, the command cannot be run again. elasticelasticsearch-setup-passwords
Access test
# Access without authentication will report authentication exception curl http://localhost:9200/_cat/indices # -The u parameter specifies the account number. After execution, you will be prompted to enter the password curl -u elastic http://localhost:9200/_cat/indices # -The u parameter specifies the account and password in the form of user:password curl -u elastic:123456 http://localhost:9200/_cat/indices
Set password
Modify user password: curl -XPOST -u elastic http://localhost:9200/_security/user/elastic/_password -H "Content-Type:application/json" -d "{\"password\":\"abcdefg\"}"
Forget password
If you forget your password, you can cancel the authentication first, that is, comment out the above config / ElasticSearch Add two configurations in YML, restart ElasticSearch, and find a type Delete the index of security-X to return to the original state without password authentication:
# see. Whether security-X exists or not curl http://localhost:9200/_cat/indices | grep ".security" # Delete index, here I am security-7 curl -XDELETE http://localhost:9200/.security-7
kibana associated account and password
Edit file: VI config / kibana YML, set account and password
xpack.security.enabled: true elasticsearch.username: "kibana" elasticsearch.password: "XXXXXX"
When logging in the web page, the administrator account is Kibana user
https encryption
If HTTPS connection is not configured, some Elasticsearch functions (such as token and API key) will be disabled. This security layer ensures that all communications in and out of the cluster are secure. HTTPS configuration is based on "transport layer TLS security configuration", so it requires that your cluster has been configured with transport layer security configuration.
https is encrypted in three places
- Elasticsearch transport layer communication encryption between nodes
- Elasticsearch external service https encryption
- Kibana service https encryption
Add certificate for transport layer encryption
Since each node in the Elasticsearch cluster is the server of the client and other nodes in the cluster, all transmission certificates must be client and server certificates.
Elasticsearch comes with the encryption signing certificate tool elasticsearch certutil to generate a digital certificate. The operation is as follows:
# After generating the root certificate, press enter twice bin/elasticsearch-certutil ca # Press enter three times after execution bin/elasticsearch-certutil cert --ca elastic-stack-ca.p12
Obtain TLS/SSL certificates that can be used for encrypted communication P12, create the directory config/certs, copy the certificate to the directory of config/certs, and then click config / elasticsearch The YML file configuration is as follows:
xpack.security.transport.ssl.verification_mode: certificate xpack.security.transport.ssl.keystore.path: certs/elastic-certificates.p12 xpack.security.transport.ssl.truststore.path: certs/elastic-certificates.p12
Restart all nodes in Elasticsearch cluster and apply transport layer encryption.
ElasticSearch enable https
Use the same authentication file as the transport layer here and edit config / elasticsearch YML, add the following code:
#Enable http layer encryption xpack.security.http.ssl.enabled: true xpack.security.http.ssl.keystore.path: certs/elastic-certificates.p12
Elasticsearch and Kibana encrypted connection
Use the previously generated file: elastic certificates P12, broken down into private key, public certificate and CA certificate
# Private Key private key, press enter openssl pkcs12 -in elastic-certificates.p12 -nocerts -nodes > client.key # Public Certificate, press enter openssl pkcs12 -in elastic-certificates.p12 -clcerts -nokeys > client.cer # CA Certificate is the CA that signs the public certificate. Just press enter openssl pkcs12 -in elastic-certificates.p12 -cacerts -nokeys -chain > client-ca.cer
Create a folder under the root directory of Kibana: config/certs, and put the file client cer,client. Copy key and client-ca.cer to this directory.
Edit Kibana configuration file VI config / Kibana YML, add the following configuration:
# Update Elasticsearch connection address elasticsearch.hosts: ["https://192.168.10.200:9200"] # ssl encryption elasticsearch.ssl.certificate: config/certs/client.cer elasticsearch.ssl.key: config/certs/client.key elasticsearch.ssl.certificateAuthorities: [ "config/certs/client-ca.cer" ] elasticsearch.ssl.verificationMode: certificate
Restart kibana, log in and request Elasticsearch to confirm whether it is operable.
Kibana turns on https
Reuse Elasticsearch digital certificate and edit Kibana configuration file VI config / Kibana YML, add the following:
server.ssl.enabled: true server.ssl.certificate: config/certs/client.cer server.ssl.key: config/certs/client.key
Restart kibana service and you can https://localhost:5601 Access kibana UI to operate.
proposal
- https recommends that only Kibana's https access be enabled. It is not recommended to enable https function for Elasticsearch service and communication between nodes. In the function test, Elasticsearch failed to start due to ssl encryption.
summary
- The installation and configuration process is cumbersome. Installing it once in sequence is conducive to understanding the principle of Elasticsearch+Kibana. The latest version 8 has just been released, which simplifies the installation process, but the release time is short and there are bug s, so it is not recommended to use it.