1, Introduction to SSH
SSH is the abbreviation of Secure Shell. SSH is a security protocol based on the application layer. SSH is a reliable protocol designed to provide security for remote login sessions and other network services. Using SSH protocol can effectively prevent information disclosure in the process of remote management. SSH was originally a program on UNIX system, and then quickly extended to other operating platforms. SSH can make up for loopholes in the network when used correctly. SSH client is applicable to a variety of platforms.
Traditional network service programs, such as FTP, pop and Telnet, are inherently insecure, because they transmit passwords and data in plaintext on the network. People with ulterior motives can easily intercept these passwords and data. Moreover, the security verification methods of these service programs also have their weaknesses, that is, they are vulnerable to the attack of "man-in-the-middle". The so-called "middleman" attack means that the "middleman" pretends to be a real server to receive the data you send to the server, and then pretends to be you to send the data to the real server. After the data transmission between the server and you is tampered with by the "middleman", there will be serious problems. By Using SSH, you can encrypt all the transmitted data, so that the "man in the middle" attack can not be realized, and it can also prevent DNS spoofing and IP spoofing. Another additional advantage of Using SSH is that the transmitted data is compressed, so it can speed up the transmission speed. SSH has many functions. It can not only replace Telnet, but also provide a safe "channel" for FTP, pop and even PPP.
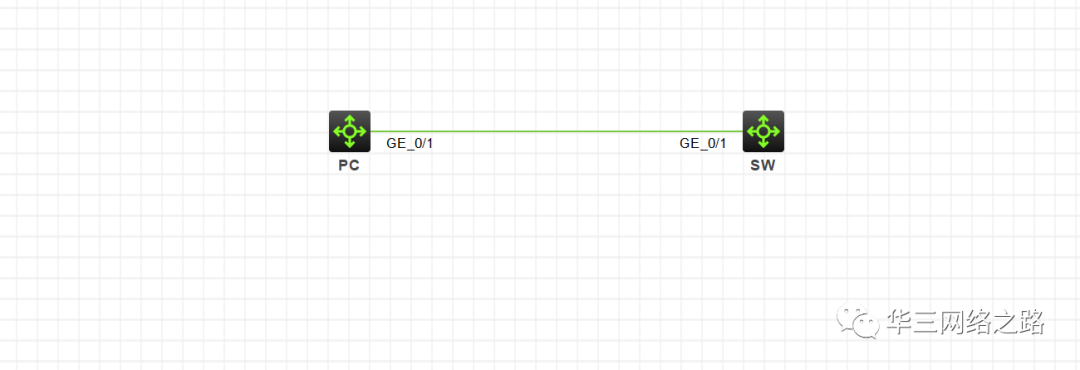
2, Experimental topology
3, Configuration requirements
The PC can remotely manage the switch of the computer room through SSH protocol in the intranet. In this experimental environment, a switch is used to simulate PC.
4, Configuration steps
1. Start SSH service on SW
[SW]ssh server enable
2. Configure the user name and password of ssh service
User name admin, password admin
[SW]local-user admin New local user added. [SW-luser-manage-admin]password simple admin [SW-luser-manage-admin]
3. Change the user's permission to network management level
Network admin is the most senior administrator privilege
[SW-luser-manage-admin]authorization-attribute user-role network-admin
4. Configure the protocol that the user can manage as ssh
[SW-luser-manage-admin]service-type ? ftp FTP service http HTTP service type https HTTPS service type pad X.25 PAD service ssh Secure Shell service telnet Telnet service terminal Terminal access service [SW-luser-manage-admin]service-type ssh [SW-luser-manage-admin]quit
5. Set the authentication mode of SSH client login user interface to scheme mode
[SW]line vty 0 63 [SW-line-vty0-63]authentication-mode scheme [SW-line-vty0-63]quit [SW]
6. Configure IP address to make PC and switch interworking in Intranet
[SW]interface Vlan-interface 1 [SW-Vlan-interface1]ip a 10.1.1.1 24 [SW-Vlan-interface1]quit [SW]
[PC]interface Vlan-interface 1 [PC-Vlan-interface1]ip a 10.1.1.2 24 [PC-Vlan-interface1]quit [PC]
5, Configuration verification
<PC>ssh2 10.1.1.1 Username: admin Press CTRL+C to abort. Connecting to 10.1.1.1 port 22. admin@10.1.1.1's password: Enter a character ~ and a dot to abort. ****************************************************************************** * Copyright (c) 2004-2017 New H3C Technologies Co., Ltd. All rights reserved.* * Without the owner's prior written consent, * * no decompiling or reverse-engineering shall be allowed. * ****************************************************************************** <SW>
explain
ssh, telnet and other protocols are very simple, but almost every project must be configured. Therefore, you can write the configuration script in advance, change the IP, user name and password in the script, and brush the script directly when you use it.
The script is as follows:
# line vty 0 63 authentication-mode scheme user-role network-operator # ssh server enable # local-user admin class manage password simple admin service-type ssh authorization-attribute user-role network-admin #
Attachment:
Follow me to get this configuration project, more configuration cases, the latest film and television and common office software
