In the previous series of tutorials, we have introduced a lot about the various usages in the Spring Boot configuration file.
These configuration related knowledge are provided by Spring Boot natively. The function we will introduce today is not supported by Spring Boot natively, but it is very useful: encryption of configuration content.
Why encrypt?
Under normal circumstances, in order to facilitate the switching environment, we will store information about the environment in the configuration file, such as mysql's account password, redis account password, Alipay, WeChat key, and so on.
This information is extremely sensitive information. Once leaked, it will cause great losses. Therefore, general developers will further encrypt the configuration file to avoid these sensitive information being directly obtained by criminals.
I Introducing jasypt
Next we will use https://github.com/ulisesbocchio/jasypt-spring-boot This open source project provides the implementation and plug-ins to help us easily complete the encryption of configuration information.
Step 1: create a basic Spring Boot project (if you don't know it yet, you can refer to this article: quick get start)
Step 2: introduce jasypt
<dependency>
<groupId>com.github.ulisesbocchio</groupId>
<artifactId>jasypt-spring-boot-starter</artifactId>
<version>3.0.3</version>
</dependency>Step 3: encrypt the user name and password of the database
@Test
public void contextLoads() {
BasicTextEncryptor textEncryptor = new BasicTextEncryptor();
// Salt required for encryption
textEncryptor.setPassword("10qyubgc");
// Data to be encrypted (user name or password of the database)
String username = textEncryptor.encrypt("root");
String password = textEncryptor.encrypt("password");
System.out.println("username:"+username);
System.out.println("password:"+password);
}Console output:
username:xkPw7rH78Y+4VORyB/7Rhw== password:DTlViR/goGloKmaFI1DBE17+lchmiA3O
Use jasypt jar package for encryption
java -cp jasypt-1.9.2.jar org.jasypt.intf.cli.JasyptPBEStringEncryptionCLI password=10qyubgc algorithm=PBEWithMD5AndDES input=root
Console output:
----ENVIRONMENT----------------- Runtime: Oracle Corporation Java HotSpot(TM) 64-Bit Server VM 25.171-b11 ----ARGUMENTS------------------- input: root algorithm: PBEWithMD5AndDES password: 10qyubgc ----OUTPUT---------------------- xkPw7rH78Y+4VORyB/7Rhw==
Copy the results under - OUTPUT -
2. Configuration file
Configure the generated encryption string enc (encryption string) to application In YML
server:
port: 8090
spring:
datasource:
url: jdbc:mysql://localhost:3306/test?serverTimezone=UTC&useUnicode=true&characterEncoding=utf-8&useSSL=true
username: ENC(xkPw7rH78Y+4VORyB/7Rhw==)
password: ENC(DTlViR/goGloKmaFI1DBE17+lchmiA3O)
data-username: com.mysql.cj.jdbc.Driver
jpa:
show-sql: true
database-platform: org.hibernate.dialect.MySQL5InnoDBDialect
database: MYSQL
hibernate:
ddl-auto: update
jasypt:
encryptor:
password: 10qyubgc # Salt required for encryption
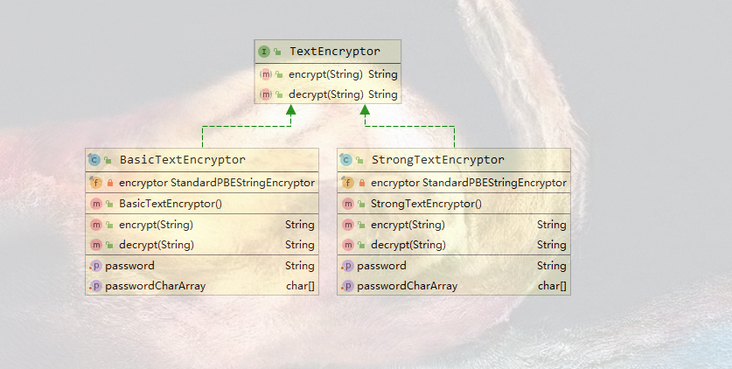
#algorithm: PBEWithMD5AndDES # The default encryption method is PBEWithMD5AndDES, which can be changed to PBEWithMD5AndTripleDESThe corresponding classes of encryption methods are BasicTextEncryptor and StrongTextEncryptor
private final StandardPBEStringEncryptor encryptor = new StandardPBEStringEncryptor();
public BasicTextEncryptor() {
this.encryptor.setAlgorithm("PBEWithMD5AndDES");
}private final StandardPBEStringEncryptor encryptor = new StandardPBEStringEncryptor();
public StrongTextEncryptor() {
this.encryptor.setAlgorithm("PBEWithMD5AndTripleDES");
}
3. Configure salt during deployment
In order to prevent salt from leaking, the password is solved You can use the command to pass in the salt value when the project is deployed
java -jar -Djasypt.encryptor.password=10qyubgc xxx.jar
Configure the salt value in the environment variable
open/etc/profile file
vim /etc/profile
Insert at the end of the file
export JASYPT_PASSWORD = 10qyubgc
compile
source /etc/profile
function
java -jar -Djasypt.encryptor.password=${JASYPT_PASSWORD} xxx.jarAt this time, the configuration file is encrypted and sensitive information is protected.